Takie to trochę śmieszne ale na stronie producenta
 .
.
Zaloguj
lub
Zarejestruj się
aby zobaczyć!
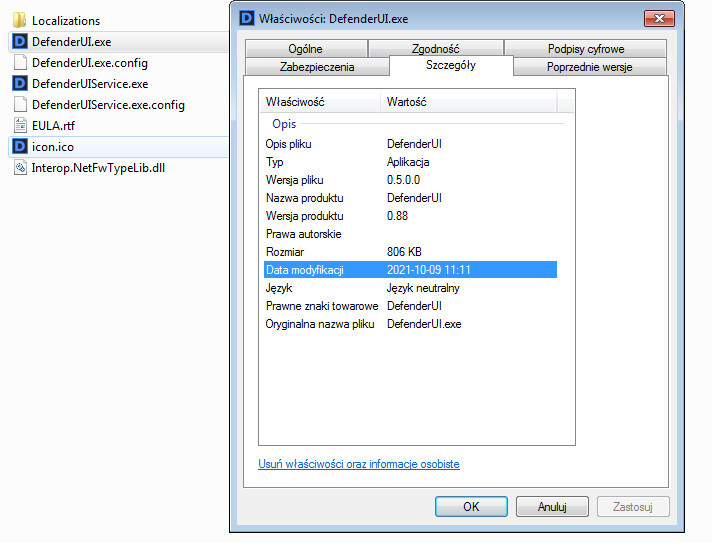
są screeny z wersji 1.0.0 której jeszcze nie ma , a jak kliknie się pobieranie to pobiera wersję 0.50 beta  .
.
Ostatnia edycja: